Introducción
FreeIPA (Identity, Policy, and Audit) es una solución de gestión de identidad y autenticación que proporciona una implementación centralizada de Kerberos, LDAP, DNS y políticas de acceso. Su arquitectura permite desplegar un servidor maestro y configurar réplicas para mejorar la disponibilidad y resiliencia del sistema.
Este documento describe el proceso completo de instalación y configuración de un servidor FreeIPA maestro, así como la implementación de una réplica para asegurar redundancia y balanceo de carga en la infraestructura.
1. Objetivo del documento
- Parte 1: Instalación y configuración de FreeIPA en el servidor maestro.
- Parte 2: Configuración de una réplica para garantizar la continuidad del servicio y la sincronización de datos entre servidores.
1.1. Arquitectura de FreeIPA
La configuración de FreeIPA sigue un modelo jerárquico donde un servidor maestro administra la base de datos LDAP y proporciona servicios centrales de autenticación. Las réplicas permiten la distribución de cargas y aseguran la disponibilidad del servicio en caso de fallos del nodo principal.
1.2 Componentes clave de FreeIPA:
- LDAP (389 Directory Server): Almacena la información de usuarios, grupos y políticas de acceso.
- Kerberos: Proporciona autenticación segura basada en tickets.
- DNS: Gestiona la resolución de nombres y permite la integración con Kerberos.
- Certificados (Dogtag CA): Maneja la autoridad certificadora para la infraestructura de claves públicas (PKI).
1.3 Resumen del proceso
1. Instalación del servidor maestro
- Configuración del hostname y resolución DNS.
- Instalación de los paquetes de FreeIPA.
- Configuración inicial del servidor IPA.
- Verificación de la instalación y servicios principales.
2. Implementación de la réplica
- Unión de la réplica al dominio FreeIPA.
- Instalación de los paquetes en la réplica.
- Configuración y sincronización con el maestro.
- Validación de la réplica y prueba de replicación de datos.
Con este manual, se busca establecer una infraestructura robusta de FreeIPA, garantizando una administración centralizada de identidades y autenticación en un entorno seguro y escalable.
2. Requisitos Previos
2.1. Requisitos del Sistema
Antes de comenzar la instalación, asegúrese de que su sistema cumpla con los siguientes requisitos:
- Sistema Operativo: os servidores con RHEL/CentOS/Rocky Linux (uno para el maestro y otro para la réplica).
- DNS: Resolución de nombres correctamente configurada en ambos servidores.
- Memoria RAM: Mínimo 4 GB (recomendado 8 GB o más)
- Espacio en Disco: Mínimo 20 GB (dependiendo del número de usuarios y servicios habilitados)
- CPU: Al menos 2 vCPUs
- Acceso Root: Se requiere acceso de superusuario
2.2. Configuración de Red
- Nombre de host configurado correctamente:
hostnamectl set-hostname srvlrofipam01.redorbita.local2.3. Deshabilitar SELinux y Firewalld (Opcional, pero recomendado para pruebas)
Paso 1: Preparar el sistema
- Instalar el sistema operativo (Rocky Linux recomendado):
sudo dnf update -y
sudo hostnamectl set-hostname srvlrofipam01.redorbita.local - Verificar que el FQDN esté correctamente configurado:
hostname -fAgregar la IP y el FQDN en /etc/hosts:
echo "192.168.1.100 srvlrofipam01.redorbita.local srvlrofipam01
2.3. Deshabilitar SELinux y Firewalld (Opcional, pero recomendado para pruebas)
setenforce 0
sed -i 's/SELINUX=enforcing/SELINUX=permissive/' /etc/selinux/config
systemctl stop firewalld
systemctl disable firewalldPaso 2: Instalación de FreeIPA
-
Instalar los paquetes necesarios:
sudo dnf install ipa-server ipa-server-dns -y
3. Instalación de FreeIPA
3.1. Actualizar el Sistema
Antes de instalar FreeIPA, es recomendable actualizar el sistema:
Instalar y configurar FreeIPA:
- Ejecuta la instalación interactiva:
sudo yum update -y3.2. Instalar los Paquetes Necesarios
Ejecutar el siguiente comando para instalar FreeIPA y sus dependencias:
sudo yum install -y @idm:DL1 freeipa-server freeipa-server-dns4.1. Configurar el Servidor FreeIPA
Ejecutar el siguiente comando para iniciar la configuración:
sudo ipa-server-install --setup-dns --allow-zone-overlapSe le solicitará configurar:
- Realm:
REDORBITA.LOCAL - Dirección del Servidor:
srvlrofipam01.redorbita.local - Contraseña de Admin: Establecer una contraseña segura
- Habilitar DNS:
Sí
Output:
The log file for this installation can be found in /var/log/ipaserver-install.log
==============================================================================
This program will set up the IPA Server.
Version 4.12.2
This includes:
* Configure a stand-alone CA (dogtag) for certificate management
* Configure the NTP client (chronyd)
* Create and configure an instance of Directory Server
* Create and configure a Kerberos Key Distribution Center (KDC)
* Configure Apache (httpd)
* Configure SID generation
* Configure the KDC to enable PKINIT
To accept the default shown in brackets, press the Enter key.
Do you want to configure integrated DNS (BIND)? [no]: YES
Enter the fully qualified domain name of the computer
on which you're setting up server software. Using the form
<hostname>.<domainname>
Example: master.example.com
Server host name [srvlrofipam01.redorbita.local]:
Warning: skipping DNS resolution of host srvlrofipam01.redorbita.local
The domain name has been determined based on the host name.
Please confirm the domain name [redorbita.local]:
The kerberos protocol requires a Realm name to be defined.
This is typically the domain name converted to uppercase.
Please provide a realm name [REDORBITA.LOCAL]:
Certain directory server operations require an administrative user.
This user is referred to as the Directory Manager and has full access
to the Directory for system management tasks and will be added to the
instance of directory server created for IPA.
The password must be at least 8 characters long.
Directory Manager password:
Password (confirm):
The IPA server requires an administrative user, named 'admin'.
This user is a regular system account used for IPA server administration.
IPA admin password:
Password (confirm):
Checking DNS domain redorbita.local., please wait ...
Invalid IP address fe80::c29d:f925:14c8:4b9e for srvlrofipam01.redorbita.local: cannot use link-local IP address fe80::c29d:f925:14c8:4b9e
Invalid IP address fe80::501d:46ec:4100:f9dc for srvlrofipam01.redorbita.local: cannot use link-local IP address fe80::501d:46ec:4100:f9dc
Do you want to configure DNS forwarders? [yes]: yes
Following DNS servers are configured in /etc/resolv.conf: 10.0.2.3, 212.230.135.1, 212.230.135.2
Do you want to configure these servers as DNS forwarders? [yes]: yes
All detected DNS servers were added. You can enter additional addresses now:
Enter an IP address for a DNS forwarder, or press Enter to skip:
DNS forwarders: 10.0.2.3, 212.230.135.1, 212.230.135.2
Checking DNS forwarders, please wait ...
Do you want to search for missing reverse zones? [yes]:
Checking DNS domain 2.0.10.in-addr.arpa., please wait ...
Checking DNS domain 1.168.192.in-addr.arpa., please wait ...
Do you want to create reverse zone for IP 10.0.2.15 [yes]:
Please specify the reverse zone name [2.0.10.in-addr.arpa.]:
Checking DNS domain 2.0.10.in-addr.arpa., please wait ...
Do you want to create reverse zone for IP 192.168.1.140 [yes]:
Please specify the reverse zone name [1.168.192.in-addr.arpa.]:
Checking DNS domain 1.168.192.in-addr.arpa., please wait ...
Using reverse zone(s) 2.0.10.in-addr.arpa., 1.168.192.in-addr.arpa.
Trust is configured but no NetBIOS domain name found, setting it now.
Enter the NetBIOS name for the IPA domain.
Only up to 15 uppercase ASCII letters, digits and dashes are allowed.
Example: EXAMPLE.
NetBIOS domain name [REDORBITA]:
Do you want to configure chrony with NTP server or pool address? [no]: yes
Enter NTP source server addresses separated by comma, or press Enter to skip: ntp.roa.es, hora.roa.es, ntp.rediris.es, 0.es.pool.ntp.org, 1.es.pool.ntp.org, time.google.com
Enter a NTP source pool address, or press Enter to skip: es.pool.ntp.org
The IPA Master Server will be configured with:
Hostname: srvlrofipam01.redorbita.local
IP address(es): 10.0.2.15, 192.168.1.140
Domain name: redorbita.local
Realm name: REDORBITA.LOCAL
The CA will be configured with:
Subject DN: CN=Certificate Authority,O=REDORBITA.LOCAL
Subject base: O=REDORBITA.LOCAL
Chaining: self-signed
BIND DNS server will be configured to serve IPA domain with:
Forwarders: 10.0.2.3, 212.230.135.1, 212.230.135.2
Forward policy: only
Reverse zone(s): 2.0.10.in-addr.arpa., 1.168.192.in-addr.arpa.
NTP server: ntp.roa.es
NTP server: hora.roa.es
NTP server: ntp.rediris.es
NTP server: 0.es.pool.ntp.org
NTP server: 1.es.pool.ntp.org
NTP server: time.google.com
NTP pool: es.pool.ntp.org
Continue to configure the system with these values? [no]: yes
The following operations may take some minutes to complete.
Please wait until the prompt is returned.
Adding [10.0.2.15 srvlrofipam01.redorbita.local] to your /etc/hosts file
Adding [192.168.1.140 srvlrofipam01.redorbita.local] to your /etc/hosts file
Disabled p11-kit-proxy
Synchronizing time
Configuration of chrony was changed by installer.
Attempting to sync time with chronyc.
Time synchronization was successful.
Configuring directory server (dirsrv). Estimated time: 30 seconds
[1/43]: creating directory server instance
Validate installation settings ...
Create file system structures ...
Perform SELinux labeling ...
Create database backend: dc=redorbita,dc=local ...
Perform post-installation tasks ...
[2/43]: tune ldbm plugin
[3/43]: adding default schema
[4/43]: enabling memberof plugin
[5/43]: enabling winsync plugin
[6/43]: configure password logging
[7/43]: configuring replication version plugin
[8/43]: enabling IPA enrollment plugin
[9/43]: configuring uniqueness plugin
[10/43]: configuring uuid plugin
[11/43]: configuring modrdn plugin
[12/43]: configuring DNS plugin
[13/43]: enabling entryUSN plugin
[14/43]: configuring lockout plugin
[15/43]: configuring graceperiod plugin
[16/43]: configuring topology plugin
[17/43]: creating indices
[18/43]: enabling referential integrity plugin
[19/43]: configuring certmap.conf
[20/43]: configure new location for managed entries
[21/43]: configure dirsrv ccache and keytab
[22/43]: enabling SASL mapping fallback
[23/43]: restarting directory server
[24/43]: adding sasl mappings to the directory
[25/43]: adding default layout
[26/43]: adding delegation layout
[27/43]: creating container for managed entries
[28/43]: configuring user private groups
[29/43]: configuring netgroups from hostgroups
[30/43]: creating default Sudo bind user
[31/43]: creating default Auto Member layout
[32/43]: adding range check plugin
[33/43]: creating default HBAC rule allow_all
[34/43]: adding entries for topology management
[35/43]: initializing group membership
[36/43]: adding master entry
[37/43]: initializing domain level
[38/43]: configuring Posix uid/gid generation
[39/43]: adding replication acis
[40/43]: activating sidgen plugin
[41/43]: activating extdom plugin
[42/43]: configuring directory to start on boot
[43/43]: restarting directory server
Done configuring directory server (dirsrv).
Configuring Kerberos KDC (krb5kdc)
[1/11]: adding kerberos container to the directory
[2/11]: configuring KDC
[3/11]: initialize kerberos container
[4/11]: adding default ACIs
[5/11]: creating a keytab for the directory
[6/11]: creating a keytab for the machine
[7/11]: adding the password extension to the directory
[8/11]: creating anonymous principal
[9/11]: starting the KDC
[10/11]: configuring KDC to start on boot
[11/11]: enable PAC ticket signature support
Done configuring Kerberos KDC (krb5kdc).
Configuring kadmin
[1/2]: starting kadmin
[2/2]: configuring kadmin to start on boot
Done configuring kadmin.
Configuring ipa-custodia
[1/5]: Making sure custodia container exists
[2/5]: Generating ipa-custodia config file
[3/5]: Generating ipa-custodia keys
[4/5]: starting ipa-custodia
[5/5]: configuring ipa-custodia to start on boot
Done configuring ipa-custodia
[1/5]: Making sure custodia container exists
[2/5]: Generating ipa-custodia config file
[3/5]: Generating ipa-custodia keys
[4/5]: starting ipa-custodia
[5/5]: configuring ipa-custodia to start on boot
Done configuring ipa-custodia.
Configuring certificate server (pki-tomcatd). Estimated time: 3 minutes
[1/32]: configuring certificate server instance
[2/32]: stopping certificate server instance to update CS.cfg
[3/32]: backing up CS.cfg
[4/32]: Add ipa-pki-wait-running
[5/32]: secure AJP connector
[6/32]: reindex attributes
[7/32]: exporting Dogtag certificate store pin
[8/32]: disabling nonces
[9/32]: set up CRL publishing
[10/32]: enable PKIX certificate path discovery and validation
[11/32]: authorizing RA to modify profiles
[12/32]: authorizing RA to manage lightweight CAs
[13/32]: Ensure lightweight CAs container exists
[14/32]: Enable lightweight CA monitor
[15/32]: Ensuring backward compatibility
[16/32]: starting certificate server instance
[17/32]: configure certmonger for renewals
[18/32]: requesting RA certificate from CA
[19/32]: publishing the CA certificate
[20/32]: adding RA agent as a trusted user
[21/32]: configure certificate renewals
[22/32]: Configure HTTP to proxy connections
[23/32]: updating IPA configuration
[24/32]: enabling CA instance
[25/32]: importing IPA certificate profiles
[26/32]: migrating certificate profiles to LDAP
[27/32]: adding default CA ACL
[28/32]: adding 'ipa' CA entry
[29/32]: Recording random serial number state
[30/32]: Recording HSM configuration state
[31/32]: configuring certmonger renewal for lightweight CAs
[32/32]: deploying ACME service
Done configuring certificate server (pki-tomcatd).
Configuring directory server (dirsrv)
[1/3]: configuring TLS for DS instance
[2/3]: adding CA certificate entry
[3/3]: restarting directory server
Done configuring directory server (dirsrv).
Configuring ipa-otpd
[1/2]: starting ipa-otpd
[2/2]: configuring ipa-otpd to start on boot
Done configuring ipa-otpd.
Configuring the web interface (httpd)
[1/22]: stopping httpd
[2/22]: backing up ssl.conf
[3/22]: disabling nss.conf
[4/22]: configuring mod_ssl certificate paths
[5/22]: setting mod_ssl protocol list
[6/22]: configuring mod_ssl log directory
[7/22]: disabling mod_ssl OCSP
[8/22]: adding URL rewriting rules
[9/22]: configuring httpd
Nothing to do for configure_httpd_wsgi_conf
[10/22]: setting up httpd keytab
[11/22]: configuring Gssproxy
[12/22]: setting up ssl
[13/22]: configure certmonger for renewals
[14/22]: publish CA cert
[15/22]: clean up any existing httpd ccaches
[16/22]: enable ccache sweep
[17/22]: configuring SELinux for httpd
[18/22]: create KDC proxy config
[19/22]: enable KDC proxy
[20/22]: starting httpd
[21/22]: configuring httpd to start on boot
[22/22]: enabling oddjobd
Done configuring the web interface (httpd).
Configuring Kerberos KDC (krb5kdc)
[1/1]: installing X509 Certificate for PKINIT
Done configuring Kerberos KDC (krb5kdc).
Applying LDAP updates
Upgrading IPA:. Estimated time: 1 minute 30 seconds
[1/10]: stopping directory server
[2/10]: saving configuration
[3/10]: disabling listeners
[4/10]: enabling DS global lock
[5/10]: disabling Schema Compat
[6/10]: starting directory server
[7/10]: upgrading server
[8/10]: stopping directory server
[9/10]: restoring configuration
[10/10]: starting directory server
Done.
Restarting the KDC
dnssec-validation yes
Configuring DNS (named)
[1/13]: generating rndc key file
[2/13]: adding DNS container
[3/13]: setting up our zone
[4/13]: setting up reverse zone
[5/13]: setting up our own record
[6/13]: setting up records for other masters
[7/13]: adding NS record to the zones
[8/13]: setting up kerberos principal
[9/13]: setting up LDAPI autobind
[10/13]: setting up named.conf
created new /etc/named.conf
created named user config '/etc/named/ipa-ext.conf'
created named user config '/etc/named/ipa-options-ext.conf'
created named user config '/etc/named/ipa-logging-ext.conf'
[11/13]: setting up server configuration
[12/13]: configuring named to start on boot
[13/13]: changing resolv.conf to point to ourselves
Done configuring DNS (named).
Restarting the web server to pick up resolv.conf changes
Configuring DNS key synchronization service (ipa-dnskeysyncd)
[1/7]: checking status
[2/7]: setting up bind-dyndb-ldap working directory
[3/7]: setting up kerberos principal
[4/7]: setting up SoftHSM
[5/7]: adding DNSSEC containers
[6/7]: creating replica keys
[7/7]: configuring ipa-dnskeysyncd to start on boot
Done configuring DNS key synchronization service (ipa-dnskeysyncd).
Restarting ipa-dnskeysyncd
Restarting named
Updating DNS system records
Configuring SID generation
[1/8]: adding RID bases
[2/8]: creating samba domain object
[3/8]: adding admin(group) SIDs
[4/8]: updating Kerberos config
'dns_lookup_kdc' already set to 'true', nothing to do.
[5/8]: activating sidgen task
[6/8]: restarting Directory Server to take MS PAC and LDAP plugins changes into account
[7/8]: adding fallback group
[8/8]: adding SIDs to existing users and groups
This step may take considerable amount of time, please wait..
Done.
Configuring client side components
This program will set up IPA client.
Version 4.12.2
Using existing certificate '/etc/ipa/ca.crt'.
Client hostname: srvlrofipam01.redorbita.local
Realm: REDORBITA.LOCAL
DNS Domain: redorbita.local
IPA Server: srvlrofipam01.redorbita.local
BaseDN: dc=redorbita,dc=local
Configured /etc/sssd/sssd.conf
Systemwide CA database updated.
Adding SSH public key from /etc/ssh/ssh_host_ecdsa_key.pub
Adding SSH public key from /etc/ssh/ssh_host_ed25519_key.pub
Adding SSH public key from /etc/ssh/ssh_host_rsa_key.pub
SSSD enabled
Configured /etc/openldap/ldap.conf
Configured /etc/ssh/ssh_config
Configured /etc/ssh/sshd_config.d/04-ipa.conf
Configuring redorbita.local as NIS domain.
Client configuration complete.
The ipa-client-install command was successful
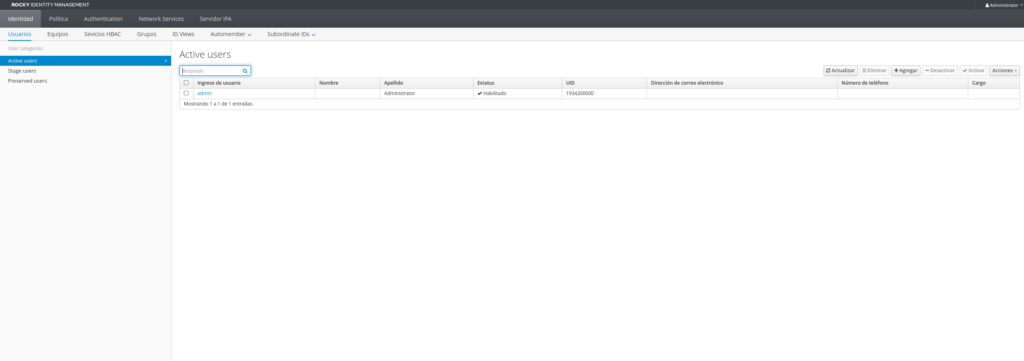
4.2. Verificar la Instalación
- Accede a la interfaz web de FreeIPA:
https://srvlrofipam01.redorbita.local/ipa/ui
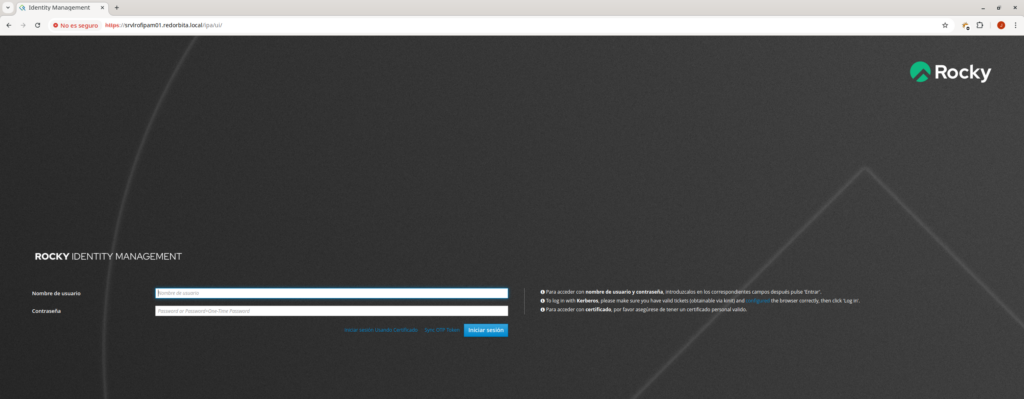
- Inicia sesión con el usuario administrador y verifica que puedas agregar usuarios, grupos y controlar políticas de acceso.
5. Configurar el servidor de réplica
5.1 Configurar el hostname
El hostname debe ser un FQDN (Fully Qualified Domain Name) y debe resolverse correctamente.
Ejemplo en la réplica:
hostnamectl set-hostname srvlrofipas02.redorbita.local
echo "192.168.1.140 srvlrofipam01.redorbita.local srvlrofipam01" >> /etc/hosts
echo "192.168.1.209 srvlrofipas02.redorbita.local srvlrofipas02" >> /etc/hosts
Prueba la resolución de nombres:
ping -c3 srvlrofipam01.redorbita.local
PING srvlrofipam01.redorbita.local (192.168.1.140) 56(84) bytes of data.
64 bytes from srvlrofipam01.redorbita.local (192.168.1.140): icmp_seq=1 ttl=64 time=0.561 ms
64 bytes from srvlrofipam01.redorbita.local (192.168.1.140): icmp_seq=2 ttl=64 time=1.55 ms
64 bytes from srvlrofipam01.redorbita.local (192.168.1.140): icmp_seq=3 ttl=64 time=0.538 ms
--- srvlrofipam01.redorbita.local ping statistics ---
3 packets transmitted, 3 received, 0% packet loss, time 2006ms
rtt min/avg/max/mdev = 0.538/0.882/1.549/0.471 ms6. Instalar los paquetes necesarios
En la réplica, instala los paquetes de FreeIPA:
sudo dnf install -y freeipa-server freeipa-server-dns freeipa-client
7. Unir la réplica al dominio FreeIPA
En la réplica, ejecuta el siguiente comando para unirla al dominio IPA:
sudo ipa-client-install --mkhomedir --server=srvlrofipam01.redorbita.local --domain=redorbita.local --realm=REDORBITA.LOCAL
Se te pedirá la contraseña del usuario admin de FreeIPA.
Output:
This program will set up IPA client.
Version 4.12.2
Autodiscovery of servers for failover cannot work with this configuration.
If you proceed with the installation, services will be configured to always access the discovered server for all operations and will not fail over to other servers in case of failure.
Proceed with fixed values and no DNS discovery? [no]: yes
Do you want to configure chrony with NTP server or pool address? [no]: yes
Enter NTP source server addresses separated by comma, or press Enter to skip: ntp.roa.es, hora.roa.es, ntp.rediris.es, 0.es.pool.ntp.org, 1.es.pool.ntp.org, time.google.com
Enter a NTP source pool address, or press Enter to skip: es.pool.ntp.org
Client hostname: srvlrofipas02.redorbita.local
Realm: REDORBITA.LOCAL
DNS Domain: redorbita.local
IPA Server: srvlrofipam01.redorbita.local
BaseDN: dc=redorbita,dc=local
NTP server: ntp.roa.es
NTP server: hora.roa.es
NTP server: ntp.rediris.es
NTP server: 0.es.pool.ntp.org
NTP server: 1.es.pool.ntp.org
NTP server: time.google.com
NTP pool: es.pool.ntp.org
Continue to configure the system with these values? [no]: yes
Synchronizing time
Configuration of chrony was changed by installer.
Attempting to sync time with chronyc.
Time synchronization was successful.
User authorized to enroll computers: admin
Password for admin@REDORBITA.LOCAL:
Successfully retrieved CA cert
Subject: CN=Certificate Authority,O=REDORBITA.LOCAL
Issuer: CN=Certificate Authority,O=REDORBITA.LOCAL
Valid From: 2025-02-19 15:44:08+00:00
Valid Until: 2045-02-19 15:44:08+00:00
Enrolled in IPA realm REDORBITA.LOCAL
Created /etc/ipa/default.conf
Configured /etc/sssd/sssd.conf
Systemwide CA database updated.
Hostname (srvlrofipas02.redorbita.local) does not have A/AAAA record.
Failed to update DNS records.
Missing A/AAAA record(s) for host srvlrofipas02.redorbita.local: 192.168.1.209.
Missing reverse record(s) for address(es): 192.168.1.209.
Adding SSH public key from /etc/ssh/ssh_host_ecdsa_key.pub
Adding SSH public key from /etc/ssh/ssh_host_ed25519_key.pub
Adding SSH public key from /etc/ssh/ssh_host_rsa_key.pub
Could not update DNS SSHFP records.
SSSD enabled
Configured /etc/openldap/ldap.conf
Configured /etc/ssh/ssh_config
Configured /etc/ssh/sshd_config.d/04-ipa.conf
Configuring redorbita.local as NIS domain.
Configured /etc/krb5.conf for IPA realm REDORBITA.LOCAL
Client configuration complete.
The ipa-client-install command was successful
8. Verifica que la unión fue exitosa:
kinit admin
Password for admin@REDORBITA.LOCAL:
ipa user-find
--------------
1 user matched
--------------
User login: admin
Last name: Administrator
Home directory: /home/admin
Login shell: /bin/bash
Principal alias: admin@REDORBITA.LOCAL, root@REDORBITA.LOCAL
UID: 1934200000
GID: 1934200000
Account disabled: False
----------------------------
Number of entries returned 1
----------------------------
Instalar la réplica del servidor FreeIPA
Ejecuta en la réplica:
sudo ipa-replica-install --setup-ca --setup-dns --forwarder=8.8.8.8
Parámetros importantes:
--setup-ca: Instala una CA subordinada en la réplica.--setup-dns: Si la réplica también actuará como DNS.--forwarder=8.8.8.8: Define un DNS forwarder (opcional).
Si no necesitas DNS, omite --setup-dns.
Output:
Password for admin@REDORBITA.LOCAL:
Lookup failed: Preferred host srvlrofipas02.redorbita.local does not provide DNS.
Could not resolve hostname srvlrofipas02.redorbita.local using DNS. Clients may not function properly. Please check your DNS setup. (Note that this check queries IPA DNS directly and ignores /etc/hosts.)
Continue? [no]: yes
Checking DNS forwarders, please wait ...
Run connection check to master
Connection check OK
Disabled p11-kit-proxy
Configuring directory server (dirsrv). Estimated time: 30 seconds
[1/40]: creating directory server instance
Validate installation settings ...
Create file system structures ...
Perform SELinux labeling ...
Create database backend: dc=redorbita,dc=local ...
Perform post-installation tasks ...
[2/40]: tune ldbm plugin
[3/40]: adding default schema
[4/40]: enabling memberof plugin
[5/40]: enabling winsync plugin
[6/40]: configure password logging
[7/40]: configuring replication version plugin
[8/40]: enabling IPA enrollment plugin
[9/40]: configuring uniqueness plugin
[10/40]: configuring uuid plugin
[11/40]: configuring modrdn plugin
[12/40]: configuring DNS plugin
[13/40]: enabling entryUSN plugin
[14/40]: configuring lockout plugin
[15/40]: configuring graceperiod plugin
[16/40]: configuring topology plugin
[17/40]: creating indices
[18/40]: enabling referential integrity plugin
[19/40]: configuring certmap.conf
[20/40]: configure new location for managed entries
[21/40]: configure dirsrv ccache and keytab
[22/40]: enabling SASL mapping fallback
[23/40]: restarting directory server
[24/40]: creating DS keytab
[25/40]: ignore time skew for initial replication
[26/40]: setting up initial replication
Starting replication, please wait until this has completed.
Update in progress, 8 seconds elapsed
Update succeeded
[27/40]: prevent time skew after initial replication
[28/40]: adding sasl mappings to the directory
[29/40]: updating schema
[30/40]: setting Auto Member configuration
[31/40]: enabling S4U2Proxy delegation
[32/40]: initializing group membership
[33/40]: adding master entry
[34/40]: initializing domain level
[35/40]: configuring Posix uid/gid generation
[36/40]: adding replication acis
[37/40]: activating sidgen plugin
[38/40]: activating extdom plugin
[39/40]: configuring directory to start on boot
[40/40]: restarting directory server
Done configuring directory server (dirsrv).
Replica DNS records could not be added on master: Insufficient access: Insufficient 'add' privilege to add the entry 'idnsname=srvlrofipas02,idnsname=redorbita.local.,cn=dns,dc=redorbita,dc=local'.
Configuring Kerberos KDC (krb5kdc)
[1/6]: configuring KDC
[2/6]: adding the password extension to the directory
[3/6]: creating anonymous principal
[4/6]: starting the KDC
[5/6]: configuring KDC to start on boot
[6/6]: enable PAC ticket signature support
Done configuring Kerberos KDC (krb5kdc).
Configuring kadmin
[1/2]: starting kadmin
[2/2]: configuring kadmin to start on boot
Done configuring kadmin.
Configuring directory server (dirsrv)
[1/3]: configuring TLS for DS instance
[2/3]: importing CA certificates from LDAP
[3/3]: restarting directory server
Done configuring directory server (dirsrv).
Configuring the web interface (httpd)
[1/22]: stopping httpd
[2/22]: backing up ssl.conf
[3/22]: disabling nss.conf
[4/22]: configuring mod_ssl certificate paths
[5/22]: setting mod_ssl protocol list
[6/22]: configuring mod_ssl log directory
[7/22]: disabling mod_ssl OCSP
[8/22]: adding URL rewriting rules
[9/22]: configuring httpd
Nothing to do for configure_httpd_wsgi_conf
[10/22]: setting up httpd keytab
[11/22]: configuring Gssproxy
[12/22]: setting up ssl
[13/22]: configure certmonger for renewals
[14/22]: publish CA cert
[15/22]: clean up any existing httpd ccaches
[16/22]: enable ccache sweep
[17/22]: configuring SELinux for httpd
[18/22]: create KDC proxy config
[19/22]: enable KDC proxy
[20/22]: starting httpd
[21/22]: configuring httpd to start on boot
[22/22]: enabling oddjobd
Done configuring the web interface (httpd).
Configuring ipa-otpd
[1/2]: starting ipa-otpd
[2/2]: configuring ipa-otpd to start on boot
Done configuring ipa-otpd.
Custodia uses 'srvlrofipam01.redorbita.local' as master peer.
Configuring ipa-custodia
[1/4]: Generating ipa-custodia config file
[2/4]: Generating ipa-custodia keys
[3/4]: starting ipa-custodia
[4/4]: configuring ipa-custodia to start on boot
Done configuring ipa-custodia.
Configuring certificate server (pki-tomcatd). Estimated time: 3 minutes
[1/33]: creating certificate server db
[2/33]: ignore time skew for initial replication
[3/33]: setting up initial replication
Starting replication, please wait until this has completed.
Update in progress, 6 seconds elapsed
Update succeeded
[4/33]: revert time skew after initial replication
[5/33]: creating ACIs for admin
[6/33]: creating installation admin user
[7/33]: configuring certificate server instance
[8/33]: stopping certificate server instance to update CS.cfg
[9/33]: backing up CS.cfg
[10/33]: Add ipa-pki-wait-running
[11/33]: secure AJP connector
[12/33]: reindex attributes
[13/33]: exporting Dogtag certificate store pin
[14/33]: disabling nonces
[15/33]: set up CRL publishing
[16/33]: enable PKIX certificate path discovery and validation
[17/33]: authorizing RA to modify profiles
[18/33]: authorizing RA to manage lightweight CAs
[19/33]: Ensure lightweight CAs container exists
[20/33]: Enable lightweight CA monitor
[21/33]: Ensuring backward compatibility
[22/33]: destroying installation admin user
[23/33]: starting certificate server instance
[24/33]: Finalize replication settings
[25/33]: configure certmonger for renewals
[26/33]: Importing RA key
[27/33]: configure certificate renewals
[28/33]: Configure HTTP to proxy connections
[29/33]: updating IPA configuration
[30/33]: enabling CA instance
[31/33]: importing IPA certificate profiles
Lookup failed: Preferred host srvlrofipas02.redorbita.local does not provide CA.
[32/33]: configuring certmonger renewal for lightweight CAs
[33/33]: deploying ACME service
Done configuring certificate server (pki-tomcatd).
Configuring Kerberos KDC (krb5kdc)
[1/1]: installing X509 Certificate for PKINIT
Done configuring Kerberos KDC (krb5kdc).
Applying LDAP updates
Upgrading IPA:. Estimated time: 1 minute 30 seconds
[1/10]: stopping directory server
[2/10]: saving configuration
[3/10]: disabling listeners
[4/10]: enabling DS global lock
[5/10]: disabling Schema Compat
[6/10]: starting directory server
[7/10]: upgrading server
[8/10]: stopping directory server
[9/10]: restoring configuration
[10/10]: starting directory server
Done.
Finalize replication settings
Restarting the KDC
dnssec-validation yes
Configuring DNS (named)
[1/9]: generating rndc key file
[2/9]: setting up our own record
[3/9]: adding NS record to the zones
[4/9]: setting up kerberos principal
[5/9]: setting up LDAPI autobind
[6/9]: setting up named.conf
created new /etc/named.conf
created named user config '/etc/named/ipa-ext.conf'
created named user config '/etc/named/ipa-options-ext.conf'
created named user config '/etc/named/ipa-logging-ext.conf'
[7/9]: setting up server configuration
[8/9]: configuring named to start on boot
[9/9]: changing resolv.conf to point to ourselves
Done configuring DNS (named).
Restarting the web server to pick up resolv.conf changes
Configuring DNS key synchronization service (ipa-dnskeysyncd)
[1/7]: checking status
[2/7]: setting up bind-dyndb-ldap working directory
[3/7]: setting up kerberos principal
[4/7]: setting up SoftHSM
[5/7]: adding DNSSEC containers
DNSSEC container exists (step skipped)
[6/7]: creating replica keys
[7/7]: configuring ipa-dnskeysyncd to start on boot
Done configuring DNS key synchronization service (ipa-dnskeysyncd).
Restarting ipa-dnskeysyncd
Restarting named
Updating DNS system records
Global DNS configuration in LDAP server is empty
You can use 'dnsconfig-mod' command to set global DNS options that
would override settings in local named.conf files
Configuring SID generation
[1/7]: adding RID bases
RID bases already set, nothing to do
[2/7]: creating samba domain object
Samba domain object already exists
[3/7]: adding admin(group) SIDs
Admin SID already set, nothing to do
Admin group SID already set, nothing to do
[4/7]: updating Kerberos config
'dns_lookup_kdc' already set to 'true', nothing to do.
[5/7]: activating sidgen task
[6/7]: restarting Directory Server to take MS PAC and LDAP plugins changes into account
[7/7]: adding fallback group
Fallback group already set, nothing to do
Done.
The ipa-replica-install command was successful
9. Validar la configuración de la réplica
Verifica la funcionalidad del servidor de réplica con:
sudo ipa-replica-manage list
Directory Manager password:
srvlrofipam01.redorbita.local: master
srvlrofipas02.redorbita.local: masteVerifica la sincronización de la base de datos LDAP:
ipa topologysegment-find domain
-----------------
1 segment matched
-----------------
Segment name: srvlrofipam01.redorbita.local-to-srvlrofipas02.redorbita.local
Left node: srvlrofipam01.redorbita.local
Right node: srvlrofipas02.redorbita.local
Connectivity: both
Comprueba la propagación de usuarios y grupos:
ipa user-find
--------------
1 user matched
--------------
User login: admin
Last name: Administrator
Home directory: /home/admin
Login shell: /bin/bash
Principal alias: admin@REDORBITA.LOCAL, root@REDORBITA.LOCAL
UID: 1934200000
GID: 1934200000
Account disabled: False
----------------------------
Number of entries returned 1
----------------------------
ipa group-find
----------------
4 groups matched
----------------
Group name: admins
Description: Account administrators group
GID: 1934200000
Group name: editors
Description: Limited admins who can edit other users
GID: 1934200002
Group name: ipausers
Description: Default group for all users
Group name: trust admins
Description: Trusts administrators group
----------------------------
Number of entries returned 4
----------------------------
10. Configurar la resolución DNS
Si ipa-replica-install mostró errores de DNS, verifica y corrige los registros:
ipa dnsrecord-add redorbita.local srvlrofipas02 --a-rec 192.168.1.209
ipa dnsrecord-add 1.168.192.in-addr.arpa 209 --ptr-rec srvlrofipas02.redorbita.local.11. Configurar servicios adicionales
Si se necesita habilitar servicios adicionales en la réplica, configura los siguientes módulos:
11.1 Habilitar autenticación Kerberos
klist
kinit admin11.2 Configurar NTP
chronyc sources:wq!