Introducción
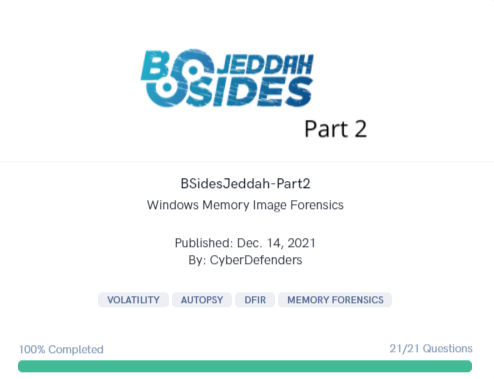
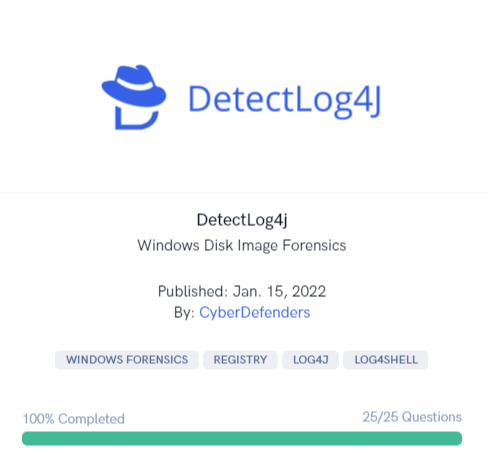
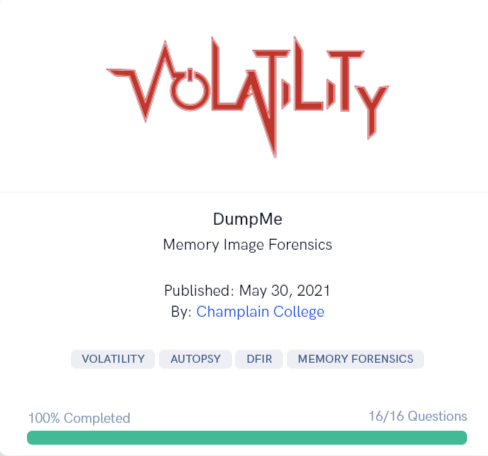
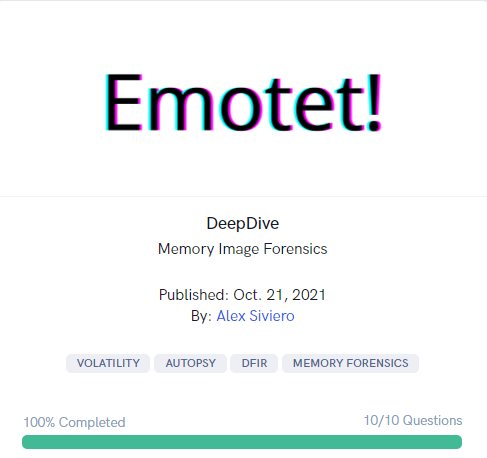
En el mundo de la informática forense, disponer de herramientas robustas y eficientes es fundamental para realizar análisis precisos y detallados. En esta entrada de blog, te explicaremos cómo activar y utilizar Volatility dentro de Autopsy para mejorar tus investigaciones forenses.
Leer más